We have seen a lot of reports lately about the malware and adware found inside apps that might be harmful to the system they are inside. Now, a new report has revealed that some more applications have been infected with a new type of malware found on the Google Play Store.
This new malware is named as the Joker malware or the Haken malware, as it is also called. As per the report, both this malware have infected as many as a dozen applications on the Play Store. It is also advised that the applications listed below should be uninstalled right away.
This new report has been revealed by security researcher Check Point which found traces of both this malware in their latest report. Check Point says that Joker is dangerous spyware which means that it can steal information from your device to a private server. On the other hand, Haken is an adware which means that it can inject ads inside your device and you can get ads on an infected device on the most annoying places.
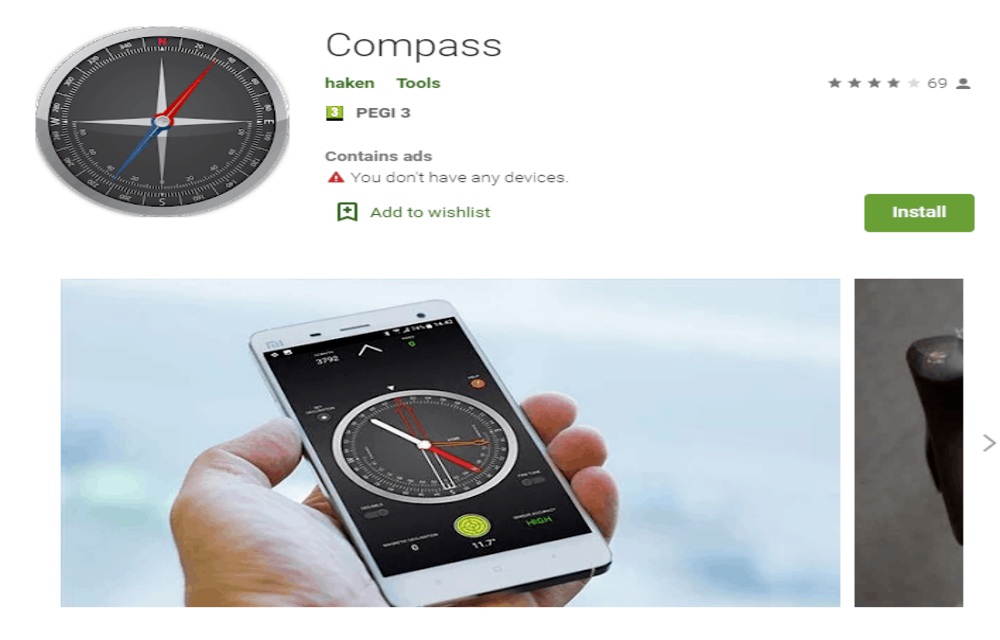
Now, Joker malware is not a new one as it was operational last year as well and at that time, it infected as many as 24 application on Android. Of the apps which have been infected by this Joker and Haken malware, one is Compass which is developed by Haken. Apart from that, you have Kids coloring, qrcode, Fruits coloring book, soccer coloring book and many others.
The worst part here is that the malware targets apps and games which are targeted towards kids and normal users. So if a device is infected, your kids could see ads inside the device which are not at all suitable for them. While these apps are still present on the Play Store, we believe that they will be removed very soon.
Leave a Reply