
Logging into the Windows and accessing mail is a regular activity of your day. Many people like me and you may become the victims of the ransomware attacks. These attacks are carried out with the help of email. The attacker uses an email as a target to spread ransomware on victims computer or network.
These kinds of attacks are exponentially increased in recent years and attacks are carried out on both individuals and business organizations. Once a computer is getting affected by the ransomware, it will get access to your computer files and folders and encrypts all your data with the attackers’ encryption key.
What is Ransomware?
Ransomware is a type of malware designed to control, alter, and encrypt all the files and folders of a computer.
As we discussed above, ransomware attacks are done by hackers and they inject the malware in the form of email attachments and infected USB drives.
According to the sources, the first known ransomware attacks occurred in the year 1989 and the victims are the healthcare industry. Now the attacks are exponentially increased and the hackers are targeting both the individuals and businesses for money.
How It Spreads?
These are the best-known ransomware types which help you to understand the level of danger when they inject in your computer.
1. CryptoLocker
CryptoLocker is ransomware was first seen in the year 2007 and spread through phishing emails. Once it spreads in your computer, it will lock all the files with encryption. The victim needs to pay the ransom amount demanded by the hacker to unlock the encrypted files.
2. GoldenEye
It remembers a movie name but it is a deadly malware which targetted oil producers in Russia and several banks.
4. WannaCry
WannaCry is a popular ransomware attack which is entered in Windows as an exploited vulnerability. The victims of the attacks are mostly hospital industry in the UK and the attacker demanded the ransomware in the form of Bitcoin.
5. Locky
Locky is first appeared in the year 2016 by a group of hackers. It has the ability to lock over more than 160+ file types with encryption method. This kind of ransomware attack is carried out on photographers, designers, developers, and engineers. After the attack, the user is unable to access the files and it needs an encryption key to decrypt the files. The attacker demands a ransom amount to give the decryption key.
6. Bad Rabbit
Bad Rabbit is a very popular type of ransomware attack where an insecure website is used to target the user. Attackers design a website which exactly looks like the genuine website. For example, an attacker creates an exact copy of the bank website and send the link through an email. The victim unknowingly clicks on the website to perform a bank transaction. Here, they collect the user ID and password of the victim.
7. Troldesh
Troldesh is yet another ransomware which uses email as a primary targeting medium. They spread via spam emails using links and attachments and demands ransom amounts from the victims.
8. Jigsaw
It is first appeared in 2016 by showing the image of a puppet from the Saw film. This ransomware deletes files by every hour and demands a ransom amount to stop the act.
9. Petya
Petya encrypts the hard drive of the victim with the help of the Master File Table (MFT). Hence, the victim is unable to access the files on the disk.
10. GandCrab
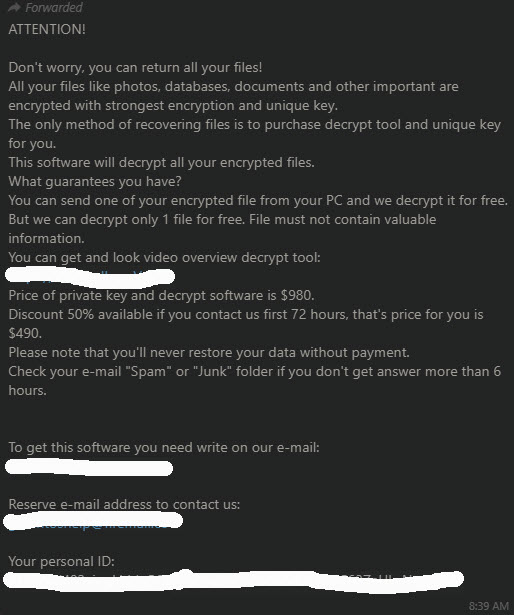
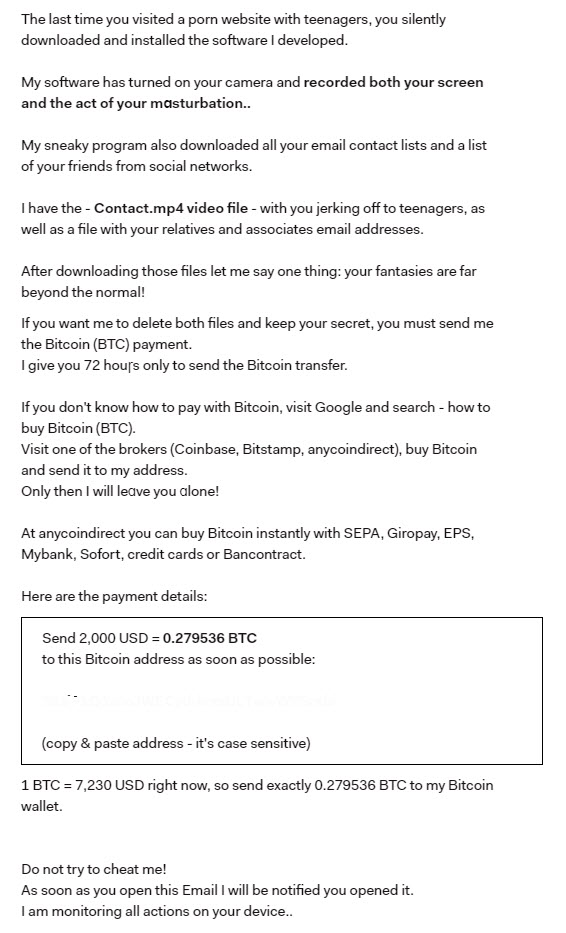
GandCrab is a type of ransomware which attacks people who are having porn-watching habits. They send a threatening email to the victim which claims that they have your webcam feed, porn watching habits and demands a ransom amount.
What to do after a ransomware attack?
After ransomware infected, your choice of options becomes more limited. These are the most possible solutions if your computer is attacked by ransomware malware.
Restoring Data
A best possible option is to restore the data from backups. If you have backups on a separate hard drive.
Recovering data using Decryption tools
There are plenty of ransomware decryption tools available to decrypt and get back the data. Before going to use these tools make sure to remove the infection from your computer. Use tools like Rakhni Decryptor, Rannoh Decryptor, and Emsisoft Ransomware Decryption Tools to recover your encrypted data.
Paying ransom amount to the attacker
Paying demanded amount is the hardest decision for anyone. I’m not advising to pay the ransom amount to the hacker but if your data is precious you need to compromise in paying the amount.
How to prevent ransomware attacks?
It is better to be safe than the let attack happens due to negligence. So why not to apply prevention methods avoid any types of virus and malware attacks on a computer. These are the best prevention methods to stop ransomware attacks on your computer.
1. Avoid spam emails
Many people click on the email links and attachments with a curiosity. The attractive images, fancy offers, shiny download images will tempt you to click on the email. Avoid spam emails and suspicious email attachments to prevent a ransomware attack.
2. Update your Operating System and Antivirus regularly
While every antivirus companies and Microsoft Windows releases new updates to handle the latest malware trials reported. An as end-user, it is your duty to keep your system up-to-date with the latest antivirus and Windows updates.
3. Use Microsoft Windows Defender
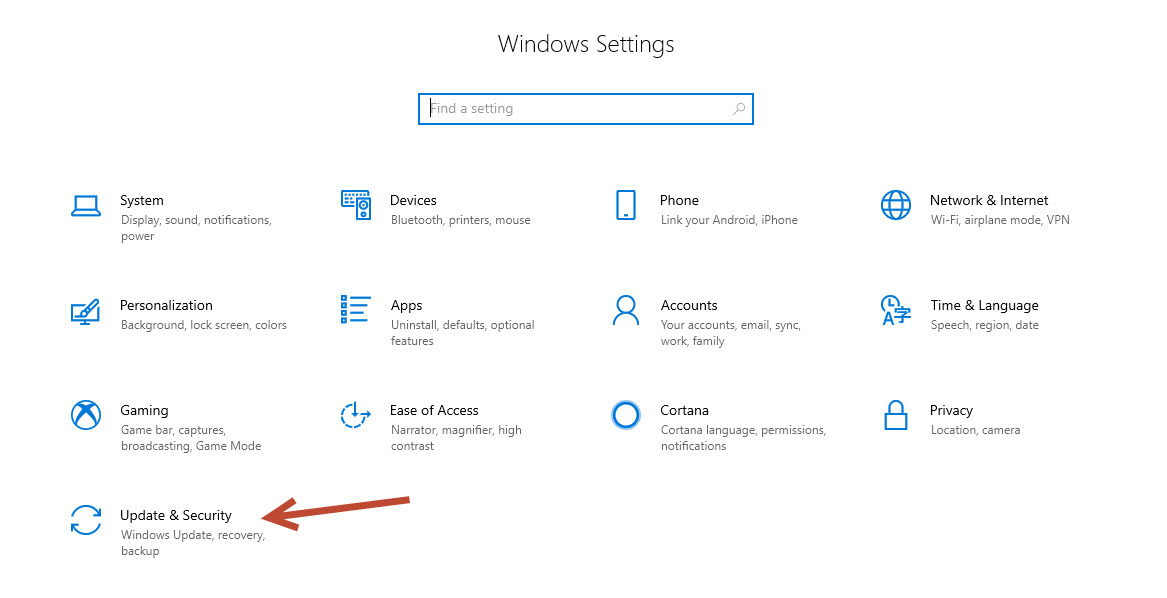
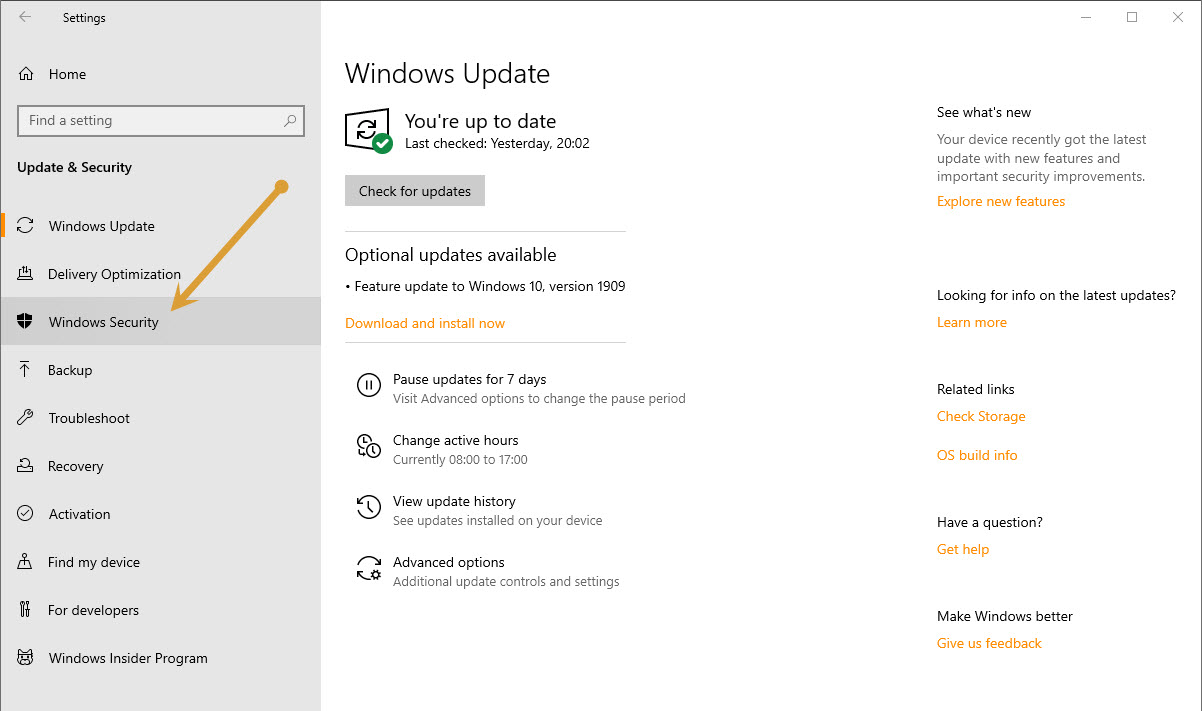
Microsoft Windows Defender has a default option of ransomware protection feature. But to avail this feature, you need to manually enable this option in Windows. Here how to enable it.
- Type Settings in the start menu.
- Click “Update & Security.”
- Now click “Windows Security.”
- Here, click on “Virus & Threat Protection” on the left pane.
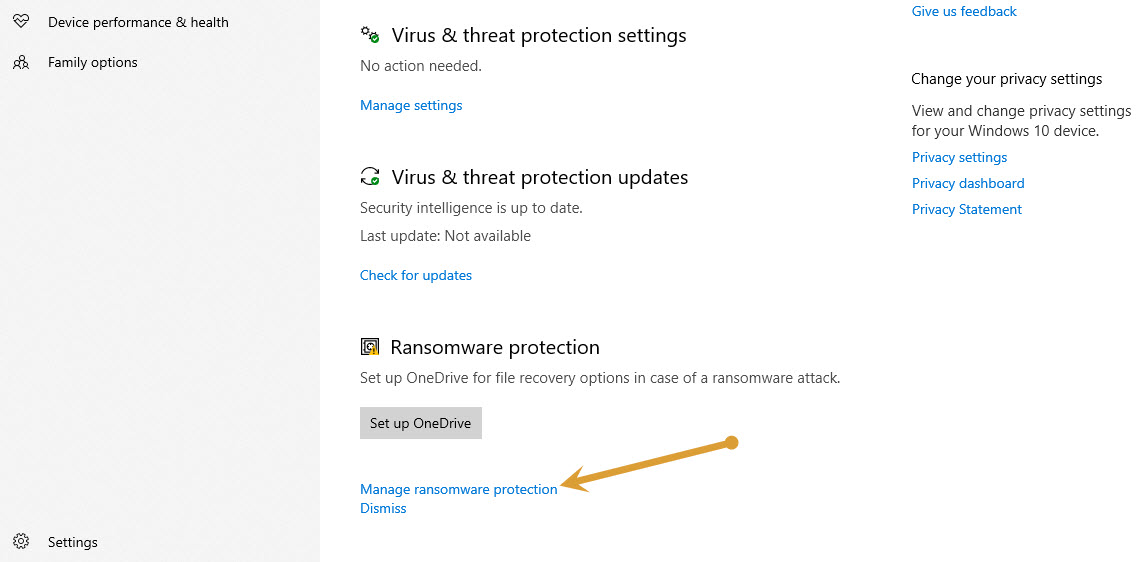
- Scroll down to the “Ransomware Protection” option.
- Click “Manage Ransomware Protection.” and proceed to the next step.
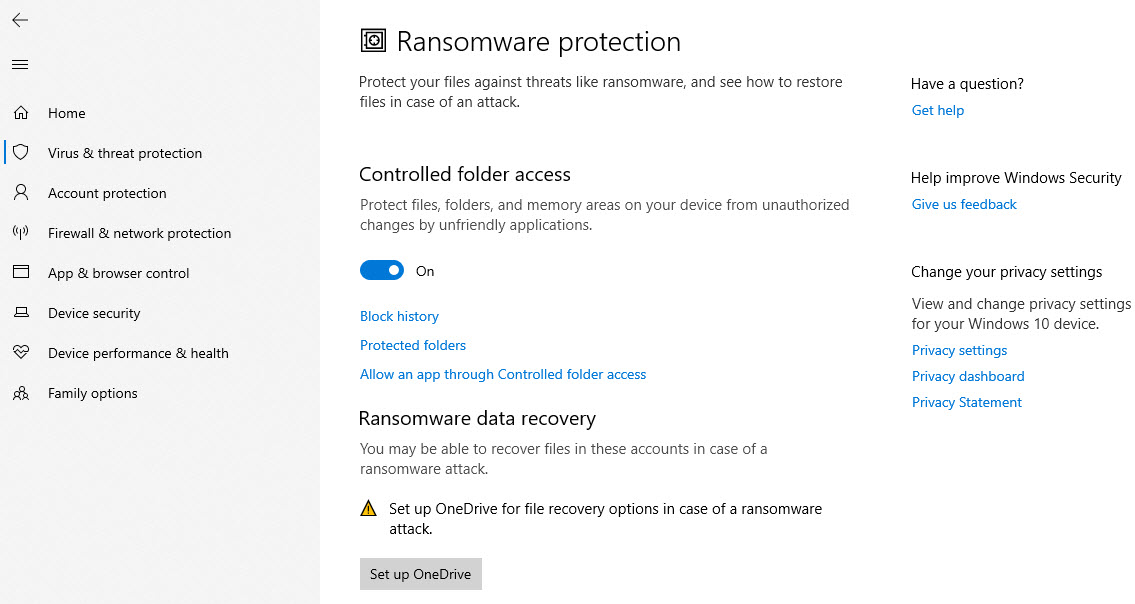
- Here enable “Controlled Folder Access” option by toggle it on.
- After you enable this option, the Windows Defender will be active in checking the ransomware entry on your Windows 10 system.
Conclusion
These are the best possible options to prevent the ransomware attacks on your computer. Make sure to enable the ransomware protection in Windows Defender and regularly update the Antivirus definitions to handle the latest attack types.
Do comment below what is your opinion about this article and which method you liked the most.

Leave a Reply